Z
IGA + JIT Access
Unified policy engine for humans and non-human identities across all tenants. Just-in-time provisioning with zero standing privileges.
IGA + JIT access; RAG-based approvals; Incident prediction.
A new species of just-in-time access management tools. Built for modern teams with AI workflows at its core, zoth sets a new standard for automated approvals, and drift detection as a single source of truth in your organisation.
Z
Unified policy engine for humans and non-human identities across all tenants. Just-in-time provisioning with zero standing privileges.
Context-aware decisions from retrieval-augmented generation. Intelligent access reviews that understand organizational context.
Detects anomalies before they escalate. Proactive threat intelligence powered by behavioral pattern analysis.
Turn policy questions, exception requests, and approval context into enforced decisions with the right owner, evidence, and duration attached.
Open/control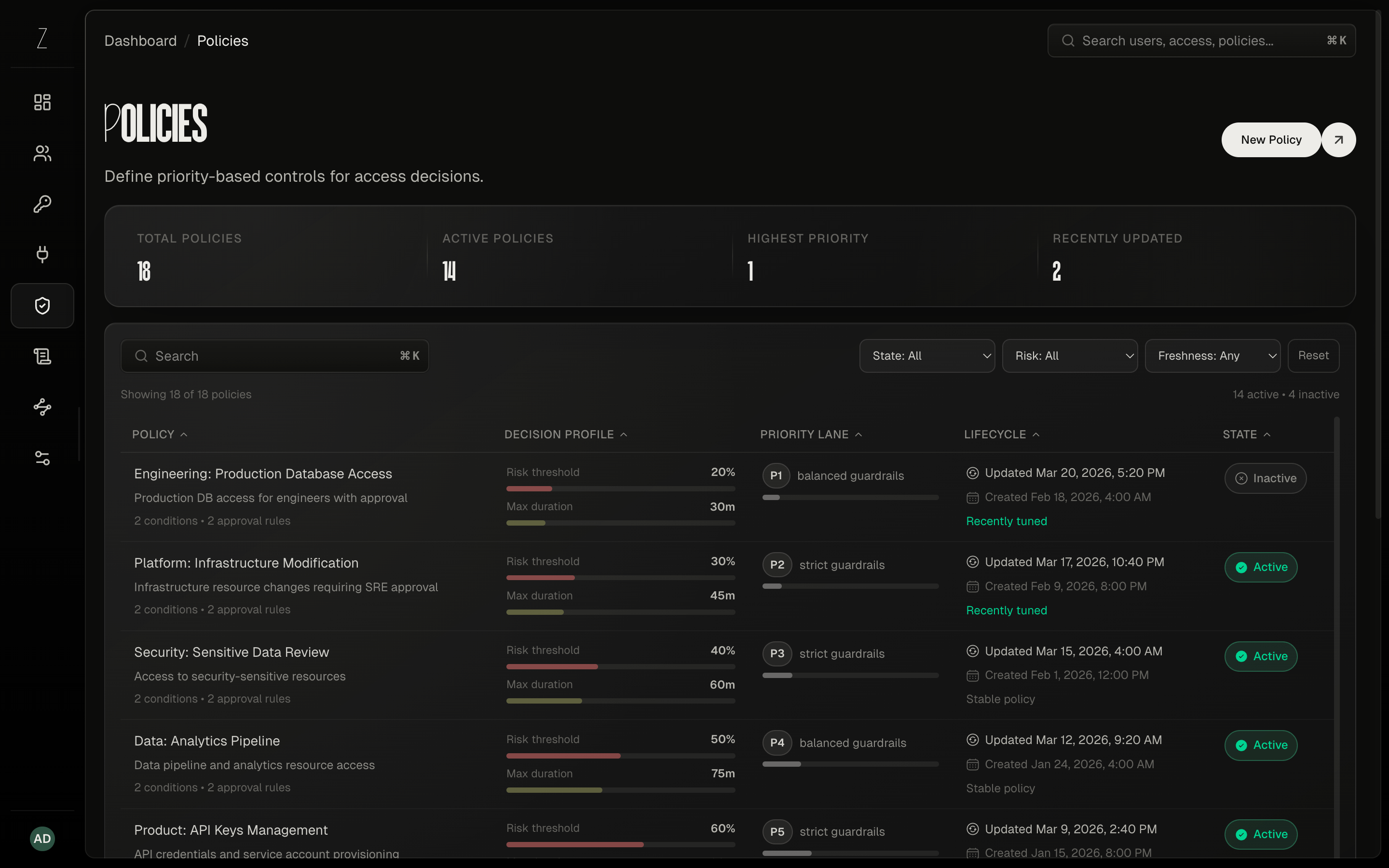
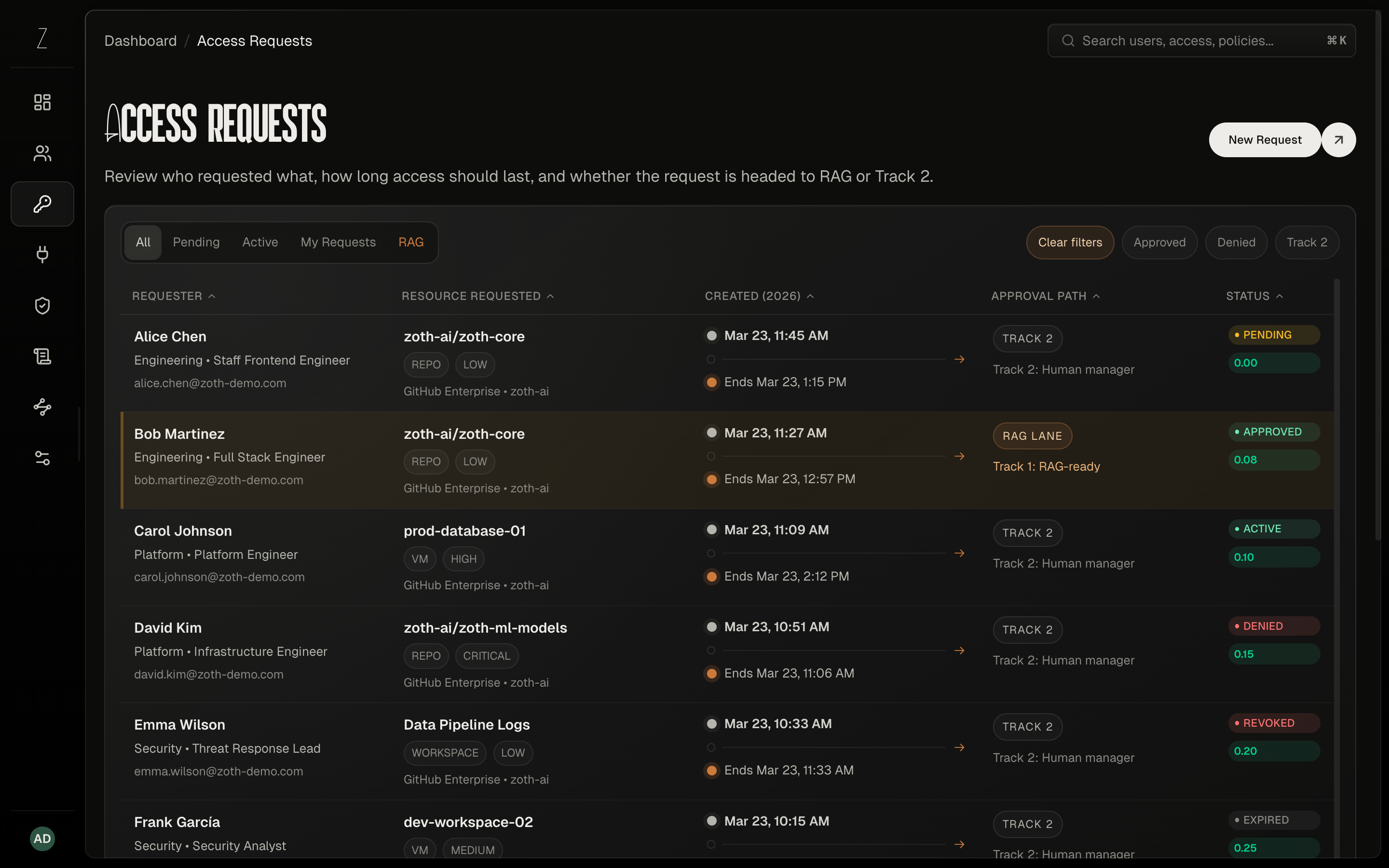
Requests are evaluated by policy, routed to the right reviewer, granted for bounded windows, and revoked on expiry while humans stay in control when sensitivity increases.
Open/automateFIG. 2.1
Request, approve, and provision access in minutes. Zoth orchestrates the entire JIT lifecycle—from policy-driven decisions to time-bound credentials to automatic expiry—so access grants become part of the system's flow, not manual overhead.
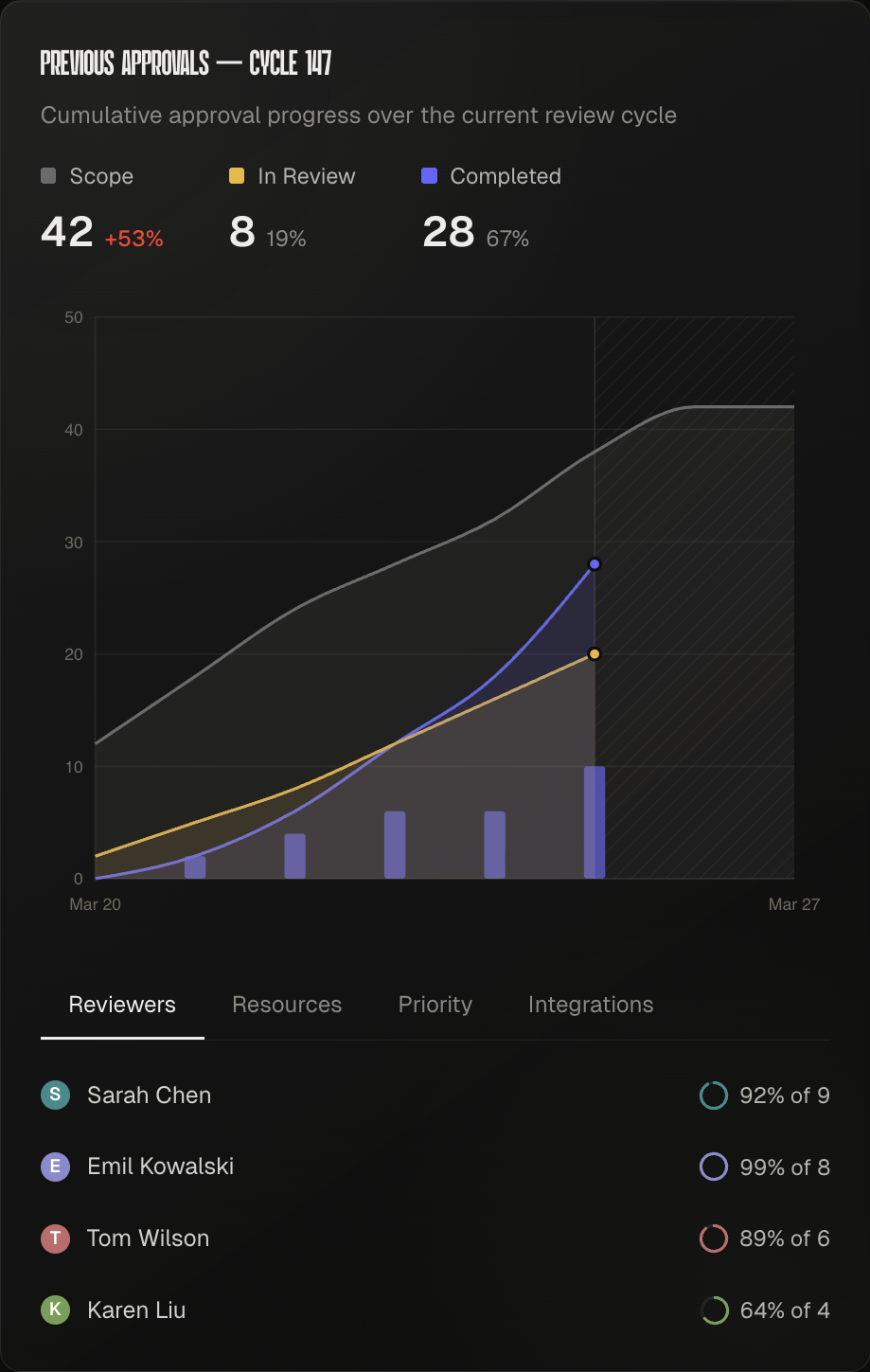
See where policy auto-routes cleanly, which managers are carrying the longest queues, and which grants will expire on time before they harden into standing access.
Slice routed requests by approver and review path to find where policy already handles low-risk grants and where humans still need to step in.
Plot approval time against requested duration to separate clean auto-routed access from sensitive requests that need deeper review before grant and revoke automation takes over.
FIG. 2.2
Zoth executes grants and revokes in downstream systems, reads their state back, and turns the gap between expected and observed access into visible drift events before standing privilege has time to settle in.
Open/enforceDense clusters stay close to policy-aligned state while the small bronze outliers mark the few reconciliations that escalated into drift alerts and remediation work.
The control plane stays authoritative, but enforcement only counts once each downstream system confirms the change or reports back a mismatch that needs human attention.
FIG. 3.3
FIG. 3.4
Map rollout windows, escalation gates, and downstream handoffs so enforcement changes land with less drift.
FIG. 3.5
Forecast which access changes are likely to miss policy deadlines so teams can intervene before drift becomes standing privilege.
Zoth keeps access state authoritative while manager commands trigger real revokes, evidence capture, and policy-safe remediation across downstream systems.
Expected access stays with Zoth. Connectors apply that state in SaaS tools, read it back continuously via a dedicated microservice, and emit auditable grant, revoke, and drift events when reality diverges.
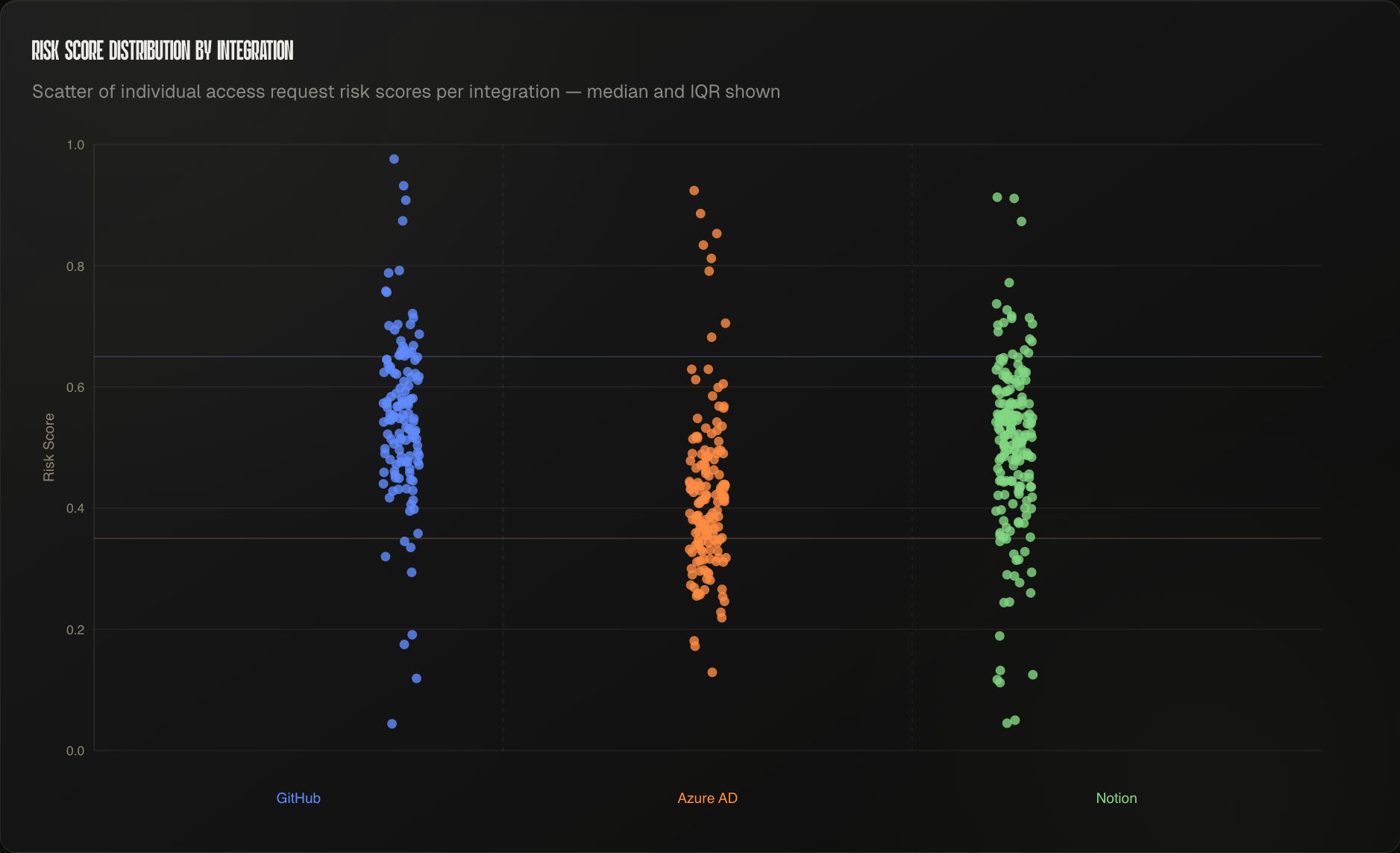
Zoth uses policy context and live telemetry to surface risk early, so reviewers can see where a request is trending before it becomes a standing privilege problem.
Open/anticipateEvery approved event inherits the state before it, so rewriting history means breaking the trust that follows.